The Role of Software Development Life Cycle in Building Secure and Robust Software
Because we live in a fast-evolving and technology-driven world, software applications have become the backbone of almost every aspect of our professional and personal lives. From online banking and eCommerce to healthcare systems and smart home devices, software development is pivotal in shaping our daily experiences and future. With this change and increased reliance on software products, cyber threats, data breaches, and system vulnerabilities have also surged.
In this article, we aim to delve deeper into the critical role that the Software Development Life Cycle (SDLC) plays in ensuring the security and robustness of a software application. We also want to offer you a comprehensive overview of the SDLC and how it integrates security considerations from the inception of the software project. If you are interested in gaining valuable insights into the indispensable practices that guarantee the security and resilience of software solutions, safeguard against potential vulnerabilities and have a smooth operations flow in an ever-evolving digital landscape, you can read the following chapters.
Understanding the Software Development Life Cycle (SDLC)
A Software Development Life Cycle is a foundational framework that guides software systems’ creation, evolution, and management. The SDLC offers a structured approach ensuring software projects are executed systematically, meeting functional requirements and quality standards. The Software Development Life Cycle (SDLC) is a systematic and methodical approach to developing, deploying, and maintaining software applications. It outlines the various stages and activities in bringing a software project from inception to completion.
The SDLC is designed to achieve a variety of interconnected and intertwined purposes. Its objectives involve multiple aspects and considerations that collectively contribute to the success of the software development process. Let’s break down the main goals of a software development life cycle: </span>
- Efficiency in software development as SDLC aims to streamline this process by breaking it down into distinct phases. Each phase has its own set of tasks, objectives, and deliverables, and this approach enables efficient resource allocation, task management, and project planning.
- Quality Assurance and Control Quality is a cornerstone. Each phase incorporates testing, validation and verification, which ensures the software meets the specific requirements, performs reliability, and adheres to quality standards.
- Minimising risks and enhanced predictability by identifying potential challenges early in the process. This proactive approach enables project teams to address issues before they escalate. Therefore, the likelihood of project delays and failures is minimised.
- Effective communication and collaboration among developers, designers, testers, and clients. The SDLC provides a structured framework for effective communication and goal alignment throughout the software development lifecycle.
Exploring the Software Development Life Cycle Phases
The Software Development Life Cycle encompasses a series of phases. Each phase contributes to the overall development process. While specific methodologies and practices might vary, the following are the foundational phases commonly found in the SDLC:
Phase 1 – Requirements Gathering
In the requirements phase, we start by closely collaborating with clients to define the functional and non-functional aspects of the software that must be fulfilled. A straightforward, comprehensive requirement-gathering process is the bedrock for the subsequent phases.
Phase 1.1 – Analysis
With the requirements in hand, we start the analysis phase. This part of the journey involves meticulously assessing gathered requirements to identify potential challenges, constraints, and opportunities. This step is a critical bridge between requirements and design, ensuring that software architecture aligns with intended objectives.
Phase 2 – Planning
In the planning phase, we establish the project’s goals and scope. We include project plans, cost estimations, resources, timelines, project requirements, and potential risks.
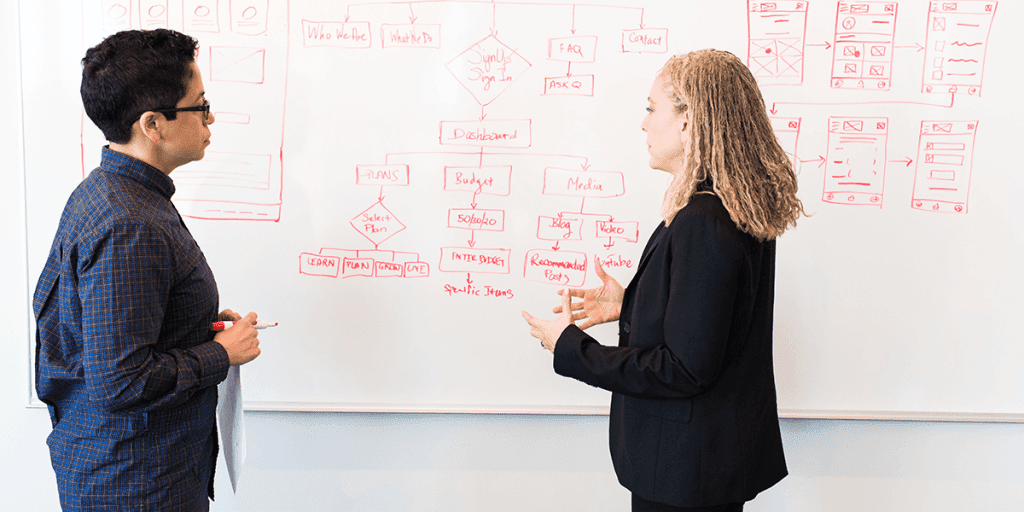
Phase 3 – Design
The software architecture and blueprint are conceptualised and documented in the design phase. We define detailed design specifications, data models, user interfaces, and system architecture because this phase sets the stage for the subsequent implementation.
Phase 4 – Implementation phase
The design is now brought to life. In the development phase, developers write the actual code, adhering to design specifications and employing coding best practices. The implementation phase transforms abstract design into tangible software components.
Phase 5 – Testing
Rigorous testing is a core element of the SDLC. The testing phase involves multiple levels, including unit testing, integration testing, system testing, and user acceptance testing. At each level, we validate different aspects of the software, ensuring its functionality, performance and alignment with the requirements.
Phase 6 – Deployment
Once the testing is successfully completed, the software is deployed to the production environment and made available to end users. In the deployment phase, we install, configure and ensure the software is ready for operational use.
Phase 7 – Maintenance
The journey of software continues after deployment. The maintenance phase involves monitoring the software in the live environment, which aims to address issues that arise. Maintenance is necessary after the development of the product to ensure its longevity and relevance in the technological landscape. An update, maintenance and enhancement checklist is a best practice to keep the health and relevance of your software.
Navigating through all the phases of the SDLC guides the development team in creating software products that meet user expectations, adhere to quality standards, and withstand the challenges posed by evolving requirements and technological advancements. We firmly stand by embracing the SDLC to deliver successful projects that drive innovation and empower user experience.
The Importance of Building Secure and Robust Software in Today’s Technology-Driven World
Data is considered one of the most valuable assets in this era, and software security has become paramount. 87% of consumers will not do business with a company if they have concerns about their security practice. Cyber threats and attacks target software vulnerabilities to access sensitive data and information, which are later exposed to unauthorised entities. No business is safe from cyber-attacks. Companies that handle user data from financial institutions to healthcare providers face severe consequences in the event of a security breach. Besides financial losses and reputational damage, data breaches can lead to legal liabilities and eroded customer trust.
Robust software is critical to ensure seamless and reliable performance. For mission-critical applications such as financial or healthcare industries, robust software systems can withstand unexpected conditions, peak loads and potential failures by reducing the risk of service interruptions and downtime.
A robust and secure solution is absolutely necessary to protect users, businesses and society from the far-reaching consequences of software vulnerabilities and inefficiencies.
With the increasing integration of technology in every aspect of our lives, the impact of software vulnerabilities and weaknesses has grown exponentially. Let’s highlight the importance of secure and robust software development:
- Data Privacy and Protection: The collection, storage, and sharing of personal and sensitive data make software systems the main targets for cybercriminals. We strongly recommend to minimise the risk of security breaches. They will lead to identity theft, financial losses, and reputational damages if they happen. A secure software development life cycle protects user data and maintains trust in technology platforms.
- Cyber Attacks and Threat Landscape: The attack vector and the threat landscape increase after the software development projects are deployed. Software security vulnerabilities are an entry point for attackers to compromise the system, steal data, and disrupt operations. A robust software design, coupled with regular updates and patches, is mandatory to block any attacks.
- Financial Implications: security incidents can result in significant financial losses for companies. From remediation costs and legal fees to fines and potential lawsuits stemming from data breaches and system failures can lead to bankruptcy. We advise you to take application security very seriously and avoid financial risks.
- Operational Disruption: In critical services such as healthcare, transportation and utilities that rely on software to function, security threats can disrupt essential services and potentially endanger lives. A robust software ensures operations’ smooth functionality, even during cyber-attacks or technical glitches.
- Reputation and Trust: Security issues can affect the reputation and trust of a business. Trust is the cornerstone of successful technology adoption. When news of a security breach or software failure comes out, it can damage a company’s reputation and erode user confidence. By prioritising security and reliability, your credibility as a business is enhanced and can foster long-term user trust.
- Regulatory Compliance: Various industries are subject to strict data protection and cybersecurity requirements. Not complying with them can lead to heavy fines and legal consequences. Developing software with security in mind helps organisations meet compliance standards.
- Early Detection and Mitigation: Identifying and addressing potential risks early in the software development environments are more cost-effective than fixing the issues after deployment. We strongly recommend incorporating security practices from the beginning of the project to reduce the risk of introducing vulnerabilities that could be exploited later.
- User Expectations: Nowadays, users expect software to be friendly, easy to use and secure. They are increasingly conscious of their digital footprint and demand protection against cyber threats. Not meeting these expectations will lead to user abandonment and finding more secure alternatives.
Addressing Security and Robustness Early: The Foundation of a Strong SDLC
To build high-quality software that is safe, secure and stable, we recommend having a systematic approach. By integrating security and robustness into each stage of the SDLC, the software development team can proactively identify and address potential vulnerabilities and minimise the risks and costs associated with software breaches and failures.
The journey towards secure and robust software begins with recognising and understanding the importance of addressing security concerns from the beginning of the development process. We do not recommend waiting until the later stages of the SDLC to address these concerns because it might result in higher costs and more significant difficulties in implementing effective solutions. By integrating security and robustness considerations early into the entire development process, developers can lay the foundation for a software product that is more resilient to attacks, less prone to vulnerabilities, and easier to maintain and update.
The Role of Each SDLC Stage in Building Secure and Robust Software
As we mentioned earlier, addressing security and robustness early in the project’s lifecycle is the foundation of a strong SDLC. Now let’s explore what is their role in each stage of the SDLC:
1. Project Requirements: Identifying and Analysing Functionality and Security Requirements
We identify and prioritise the functionality and security concerns in the gathering and requirements analysis stage. This stage involves understanding potential threats and security risks and defining user needs and expectations. The requirement analysis phase plays a pivotal role in shaping the trajectory of software development and helps the planning phase.
Functionality requirements refer to the features, capabilities, and performance expectations that the software should present. This process involves close collaboration between developers, business stakeholders, and end-users. We also use case analysis to break down the software’s intended functionality into user cases or user stories, we prioritise functionality requirements based on their importance to users and the business, and the last step is to validate everything with the stakeholders. This way, we prevent misunderstandings and ensure an alignment between expectations and development outcomes.
Security requirements must be included in the requirement phase because it helps build a strong defence against potential vulnerabilities. We consider industry-specific regulations and compliance standards that the software must adhere to, such as data protection laws, privacy regulations, and cybersecurity frameworks. We determine how sensitive data will be collected, stored, processed and transmitted and specify encryption requirements, access controls, and data retention policies. Furthermore, we define the authentication and authorisation processes, ensure secure communications protocols and define error handling and logging.
Early security integration is essential because we can mitigate risks, is more cost-efficient, guarantees user satisfaction, and the software complies with legal and regulatory requirements.
2. Planning: Creating a Security-Centric Blueprint for Resilient Software Development
We lay the foundation for secure and robust software in the Software Development Life Cycle (SDLC) planning stage. We conduct thorough risk assessments, define clear security objectives, allocate resources for security measures, and establish guidelines through security policies and standards. We are integrating security practices such as threat modelling, secure design principles, and compliance requirements to ensure security is considered from the outset.
We strategically incorporate security considerations in the planning stage to set the tone for the entire development process, creating a proactive approach to building well-equipped software to handle security challenges and instilling a culture of security consciousness.
3. Design: Incorporating Security Principles and Designing for Resilience

Software architects and designers translate requirements into a comprehensive system design in the design phase. This is also the stage where security principles are integrated into the software’s architecture and design, and decisions are made to ensure the system’s resilience against potential threats and failures. The architectural design showcases the product’s various components, encompassing internal and external communication components. Moreover, it maps out the pathways and data flow between the system components. Through the design process, the system architect must incorporate the attributes of a secure architecture to yield a design that prioritises security.
The system architecture should be a comprehensive model identifying potential areas where software flaws might emerge. This is a pivotal stage to identify and mitigate bugs and flows before moving into the implementation phase.
We focus on conducting an architecture risk analysis to identify vulnerabilities and offer tailored guidance for rectifying each flaw individually. The security team provides the suggestions necessary to fix everything. By being careful about thinking about security when designing the software and dealing with possible problems ahead of time, your business can ensure that significant issues with how the software is built do not turn into expensive problems later on.
Early security integration in the design phase will help with early prevention, reduce the attack surface, and ensures operational continuity, data protection and adaptability to dynamic environments.
4. Implementation: Writing Secure Code and Following Best Practices
Developers translate the design into actual code during the implementation stage. Writing secure code involves adhering to coding standards, using secure coding practices, and following guidelines to prevent common vulnerabilities such as injection attacks, cross-site scripting, etc. The design phase introduces half of the security issues that might arise, while the other half is presented in the implementation stage. It is critical to focus on secure code review and check the pieces of code that might cause security problems. Our security experts will look at the code and use tools to review it. However, we manually check the results after using online tools to ensure they are correct. Another way to test the code during this phase is by applying static application security testing to determine any security problem with the source code.
Regular code reviews are important because they can further enhance the quality of the codebase, identifying potential security gaps early and correcting them before they escalate into significant issues.
5. Testing: Conducting Thorough Security and Functional Testing
Thorough testing is crucial to identify vulnerabilities and ensure the software’s functionality. Security testing, including vulnerability scanning, penetration testing, and code analysis, helps detect and address security weaknesses. We perform functional testing to ensure the software behaves as intended and meets the established security and functionality requirements. Any issues discovered during testing are promptly addressed before moving to the deployment stage.
Rigorous testing to evaluate the performance and robustness of the software takes place in a controlled test environment, where our Quality Assurance team meticulously assesses the software quality and security measures from a business point of view and end-user perspective.
The testing phase lasts until every identified security issue is addressed and the product achieves the desired level of quality. This stage significantly contributes to the overall reliability and success of the software product.
6. Deployment: Ensuring a Secure Deployment Environment
The deployment phase means your software application is in a production environment and requires careful consideration of security and robustness. A secure deployment environment is mandatory to maintain the product’s integrity, availability and protect sensitive data. Even if your software is live, we strongly recommend conducting regular penetration testing to ensure the security of your product over time. To stand firm against potential attacks, the software product should have a protective mechanism beyond just relying on firewalls. We recommend implementing configuration management, access controls, and monitoring mechanisms. They are essential to maintaining the security posture of the deployed system. Moreover, continuous monitoring helps identify anomalies, potential breaches, and performance issues, allowing timely intervention and remediation.
7. Maintenance: Continuously Updating and Patching
Lastly, the last stage is the maintenance of your software because it’s a dynamic environment. Over time, it evolves, and you need to address changing user needs and emerging threats. As new vulnerabilities are discovered and new attack vectors emerge, your team of developers must remain vigilant and proactive in applying updates to keep the software secure and resilient. Continuously updating and patching the software is critical to maintaining its integrity and security. Regular maintenance involves continuous updates, bug fixes, and security patches.
Maintenance is important to mitigate vulnerabilities, reduce risks of potential breaches, data loss, and system disruptions, ensure the software’s stability, performance, and compliance, and maintain user trust.
Common Challenges and Considerations in Implementing Security and Robustness Throughout the SDLC
Integrating security and robustness throughout the Software Development Life Cycle (SDLC) is crucial to ensure that software products are resilient against threats and capable of delivering reliable performance. However, this process has its challenges and complexities. Let’s explore the most common challenges and considerations in implementing security and robustness throughout your SDLC:
1. Early Integration of Security:

- Challenge: security is integrated from the very beginning of the SDLC. Many development teams need help to prioritise security in the initial stages, leading to vulnerabilities being introduced early on.
- Consideration: We advise business owners to understand the importance of security education and training for development teams. Incorporating security requirements in the initial stages, such as during the requirement analysis and design phases, ensures that security is not an afterthought.
One in five organisations do not test their software for security vulnerabilities.
2. Balancing Security and Usability:
- Challenge: A balance between security and usability is often challenging. Rigorous security measures might lead to a tiresome user experience, potentially impacting user satisfaction and friendliness.
- Consideration: We recommend conducting thorough user-centric design and usability testing to identify solutions that offer both security and a positive user experience. Incorporating user feedback and iterative testing can help harmonise security and usability.
3. Resource Constraints:
- Challenge: Limited resources, such as time, budget, and skilled professionals, can delay the implementation of robust security measures throughout the SDLC.
- Consideration: We recommend prioritising security activities based on risk assessment. Employing automated security testing tools and leveraging external security experts through bug bounty programs or penetration testing services can help overcome resource limitations.
4. Changing Threat Landscape:
- Challenge: The threat landscape constantly evolves, with new attack vectors and vulnerabilities emerging regularly. This makes it challenging to stay ahead of potential security risks.
- Consideration: We recommend continuously monitoring security trends and updating your software regularly. Furthermore, we strongly advise you to establish a process for reviewing and updating security measures in response to emerging threats. Regular security assessments and penetration testing help identify vulnerabilities in the software.
Vulnerability scans can identify over 50,000 unique external and internal weaknesses.
5. Third-Party Dependencies:
- Challenge: Relying on third-party libraries, components, or services introduces potential security risks when those dependencies have vulnerabilities.
- Consideration: We recommend conducting thorough risk assessments of third-party dependencies, monitoring security advisories, and promptly updating dependencies with security patches.
1.5 billion users’ private information was leaked due to third-party breaches.
Our Advice – Best Practices for Secure and Robust SDLC Integration

Integrating security and robustness into the Software Development Life Cycle is mandatory to ensure the creation of secure, reliable, and high-quality software products. We want to share with you the best practices to develop and implement secure and robust SDLC:
1. Think and Implement Security Principles in Every SDLC Phase
Security must be the core principle from the outset. By embedding security as a central focal point in every decision, your development team can start building a robust and safeguarded software environment. Security considerations in the initial stages of requirements, analysing, planning and design help identify potential vulnerabilities, mitigate risks from the start, and become part of the software’s identity.
We recommend creating a proactive security strategy from threat modelling and attack vectors to risk assessments, secure design principles, code QA, regular testing, continuous monitoring and security awareness training.
2. Create a Comprehensive Policy
We strongly recommend crafting a clear policy that guides the entire development lifecycle, setting standards and protocols. This policy ensures consistency and alignment with top software testing trends. Include guidelines for secure coding, vulnerability management, code reviews, deployment, incident handling, and ongoing security training. By fostering a security-focused culture, you build a robust software development process.
Moreover, we advise you to encompass procedures for addressing security incidents and offer guidelines for continuous security training and awareness.
3. Prioritise Critical Challenges
We strongly recommend focusing on critical issues and actionable solutions rather than attempting to resolve every identified vulnerability. While newer or smaller applications might feasibly address all security concerns, the same may not hold for older or more extensive applications. Prioritising critical challenges will prove valuable, preventing security problems from entering production and systematically tackling existing vulnerabilities over time.
4. Leverage Agility in Response to Changing Threats
We strongly recommend leveraging Agile Methodologies to enable continuous security integration and deployment during custom software development. This integration empowers proactive security handling, rapid adoption of new measures, and staying ahead of emerging threats. By embracing agility, you fortify your software’s resilience against evolving challenges.
5. Foster a Mindset of Continuous Improvement
We strongly recommend employing like-minded people, given that SSDLC transforms team dynamics. It’s crucial for all parties involved to approach this evolution with receptivity. The security team should empower developers to secure their applications, embracing a growth-oriented perspective that promotes ongoing enhancement.
Creating safe and strong software has an incredible impact on a business’s success. The Software Development Life Cycle (SDLC) is a helpful guide that leads developers through all the steps of building high-quality software. From the very beginning to the final stage, the SDLC makes sure that security is a part of everything. If you need help with building strong and robust custom software with security and end-user in mind, drop us a message.
Frequently Asked Questions
The primary role of security in a Software Development Life Cycle (SDLC) is to ensure that the software being developed is built with solid defences against potential threats, vulnerabilities, and cyber attacks.
To develop a secure software development life cycle or an SSDLC, you integrate security practices and considerations into every phase of the development process.
Requirements gathering & analysis, planning, design & prototyping, development, testing, deployment, and maintenance.
Agile model, Waterfall model, DevOps.